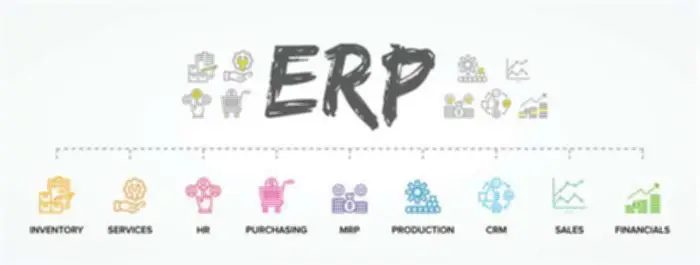
Ivanti MAM is designed to simplify mobile utility management and provide a secure setting for employees to access the applications they need to be productive. With Ivanti MAM, companies can acquire larger management over cellular purposes and reduce the danger of knowledge breaches, all while empowering workers to work more efficiently and effectively. With mobile gadgets taking middle stage in organizations, app administration can no longer be sidelined. Most organizations which may be growing to be mobile-first both present cellular units to their employees, or enable them to entry corporate knowledge from their private devices. In simple terms, it is a answer for distributing and managing functions to cellular devices.

Play Store Security And Customization
- These are additionally important, however they represent a special set of points, so I won’t be covering them on this series.
- Improved securityMAM options help to manage and protect company data on employee-owned and company-owned mobile gadgets.
- Typically, these apps embrace a mail app, a document management app and a few assorted in-house net apps.
If you have a fleet of android devices inside the workplace, you could use Android Enterprise (AE) to create a separate container inside these devices. Depending on organizations, there are situations where solely few apps need to be provisioned to finish users. Usually, these apps embody a mail app, a doc management app and a few assorted in-house web apps. Customers could not require Wi-Fi profiles to be preconfigured, or perhaps a VPN connection to be in place. Implementing a separate MAM solution increases mobile application improvement, assist, and distribution prices. Moreover, IT might want to spend extra time learning a separate device and creating greatest practices and governance over deploying and managing apps.
In response to this problem, a bunch of enterprise mobility administration (EMM) vendors fashioned the AppConfig Neighborhood in 2016. AppConfig defines tools and best practices that present an open method to configuring and securing mobile apps. This benefits users with a better out-of-the-box experience and companies with safe apps that are straightforward to combine. These are seamless to present MAM methods in the popular unified endpoint administration (UEM) merchandise of this group. Members of the AppConfig Group include BlackBerry, SAP, IBM, VMware, Jamf Software Program, MobileIron, SOTI, Cisco and Meraki. Implementing safety measures on a personal gadget looks like an overkill for employees Data Mesh, making them skeptical concerning the privateness of their personal information.
Safeguard corporate data by making use of knowledge sharing restrictions to enterprise apps on BYOD. Admins can ensure steady application security by remotely enabling required app configurations and permissions. Managed app configurations can simplify the app distribution course of by pre-configuring some of the app settings. Remotely enabling app permissions would stop customers from enabling any permissions that would open doorways for potential data leaks. IOS units have a business media asset management is generally used for container that separates work apps from private apps and restricts the move of knowledge from one space to a different. This characteristic prevents workers from opening recordsdata from managed sources in unmanaged areas.
Mobile Utility Administration allows you to distribute and manage apps without having to manage the whole gadget. Learn how we achieve exactly that on our DaaS main web page or take a glance at specifics on or function pages. Restrict devices to specific apps and features and customize the house screen using the kiosk operate. Approve store and in-house apps on a self-service portal for the convenience of the IT group and employees.
Utility Administration For Windows
This strategy, also referred to as software sandboxing, isolates an app or group of apps from different apps on a device. Data within this isolated space, generally known as a container, can’t leave, and apps throughout the container can’t work together with those on the outside. An extreme instance of containerization is dual persona technology, which creates two separate consumer interfaces — one for work and one for private use — on the same device. The benefits a company can understand with BYOD embrace decreased company hardware expenditures and elevated productivity for employees.

With MAM techniques in place, companies can remotely configure and update apps whenever they need to. This is a primary MDM feature that will be helpful all yr round but it’s also a helpful gizmo if there are any internal safety changes inside your organization. Manage the whole suite of merchandise from Zoho Office with conditional entry and app safety insurance policies for enhanced security, productiveness, and end-user experiences. Guarantee that only licensed apps and gadget features may be accessed by implementing kiosk mode. Restrict units to only a single app or a delegated set of apps and customize the home display wallpaper, icon layout, and fonts. Moreover, run apps in the background to meet dependencies whereas in single-app lockdown.
These actions are important when defending your organization information whereas enabling employees to work how and where they need. IT admins will have to have control and visibility of corporate apps and data on BYOD used by staff. A MAM resolution, similar to Microsoft Intune, provides IT the option to manage the apps that contain corporate knowledge whereas leaving personal knowledge untouched. Bring your personal device (BYOD) insurance policies are changing into extra frequent and are estimated to achieve a market value of almost $367 billion by 2022, in accordance with https://www.globalcloudteam.com/ research by Global Market Insights, Inc. However simply managing corporate apps on gadgets isn’t adequate, since personal apps put in on BYOD endpoints are an additional information breach threat for organizations.
Delivering and sustaining corporate cellular apps clearly seems as a key topics for corporations as of today.A number of best practices have emerged to reply needs from each companies and user expectations. Solely apps with built-in administration capabilities or builders who construct third-party apps suitable with a MAM platform may be managed seamlessly. The gadgets run a single or limited variety of apps that cater to employee- or customer-specific wants. Employee-facing needs can vary from stock and field service administration to move and logistics.
This is especially essential for workers that use their cellular devices for each private and skilled purposes. Containerization allows staff to keep using their phone freely whereas sustaining a sturdy degree of safety over important work-related apps. Forestall knowledge sharing between managed apps and unmanaged apps and take away all company information when the device integrity is breached. Limit backups of company data to third-party cloud services and forestall customers from installing apps from untrustworthy sources and even varied business shops. UEM developed from EMM merchandise because organizations wanted a way to handle all their endpoints — together with desktops and laptops — from one tool.
Strive Hexnode free for 14 days to safe and handle applications inside the enterprise. Also, IT will spend additional time growing finest practices and parameters for governance over testing, wrapping and deploying applications. These procedures can seem mundane and enhance cost and complexity, but both are key to a profitable MAM implementation. Strive out Hexnode UEM on your organization and enjoy all its MAM features to handle apps simply.